Good afternoon,
I need some help, I set up the VPN according to this tutorial: Site-to-Site with IPsec
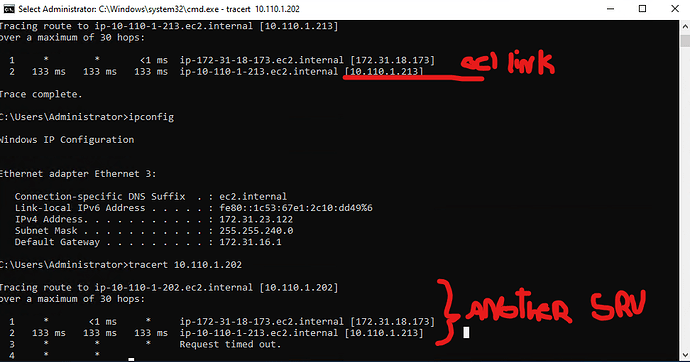
With it the link between VPC AWS and OCI is working, however I can’t get access from the AWS servers in the OCI network, on the contrary it works. And the vpn clients can access both networks.
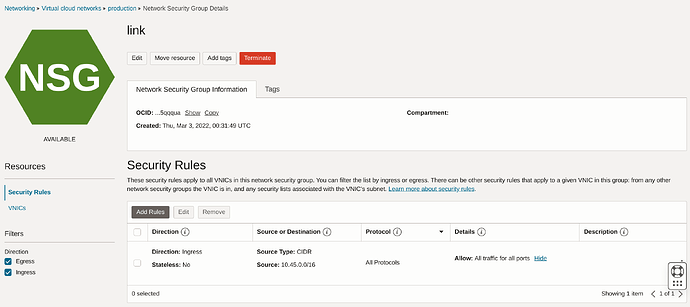
If only one side isn’t working it is most likely an issue with the Oracle Cloud firewall. You will need to permit all ingress from the Oracle VPC subnet to the Oracle pritunl-link instance. Below is an example of this being done with a Network Security Group policy but it can also be done with a Security List.
Worse still, it’s allowed, both in a security list and in the security group. What I’ve noticed is that I can access AWS on the link server in OCI, but not on the rest of the servers, even though I’ve freed the network for the servers.
It seems to be a routing problem, because the packet reaches the link server, but can’t find the server I want to reach.
And the ping command from the link server to the destination server works.
Verify that skip destination check is enabled on the VNIC and run the commands below.
sudo yum -y remove iptables-services
sudo systemctl stop firewalld.service
sudo systemctl disable firewalld.service
Yes, it’s enabled.
And my installation is running on ubuntu 22.04.3, I have disabled everything that refers to the firewall.
can anyone help?