Pritunl v1.32.4512.98 has been released. This release adds offline subscription support, single sign-on outage bypass mode, external web server NaCl based token, replicated server route advertisement support and API support for Pritunl Cloud VPC routing tables updates.
Offline Subscription
The software will now be able to maintain the subscription state for several days if there is an outage or network issue that prevents reaching the Pritunl subscription servers. This will persist even if the Pritunl service or the instance is restarted. This will ensure the services are available even if all external internet access is lost.
Single Sign-On Outage Bypass
An option to bypass single sign-on authentication has been added to the server settings. This will allow single sign-on users to connect without requiring connection to any external services. Device authentication must also be enabled to maintain secure connections. This will allow temporarily maintaining access to systems during widespread service outages while still maintaining a high level of security with TPM/Apple Secure Enclave based device authentication.
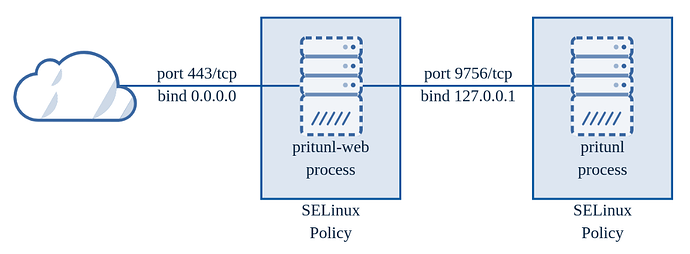
External Web Server NaCl Token
The web server for Pritunl is designed with two layers to provide a high level of protection from RCE and web framework exploits. The external pritunl-web process runs a Go based web server which parses and validates all incoming JSON data then re-serializes it and sends it to the root pritunl Python based process. Most exploits to be effective would need to exploit both the Go and Python codebases. On RHEL based distributions the external pritunl-web process is also isolated using an included SELinux policy to provide additional RCE protection. The external web server can also run as a non-root user when configured to use the systemd unit as documented in the Securing Pritunl documentation.
This update further improves this system by adding an additional NaCl signature based token to the session cookie that can be validated by the external pritunl-web process. This allows the pritunl-web process to pre-authenticate any request going to an admin API path without ever sending the request to the internal web server. This significantly reduces the attack surface of the session management in the root Python web process by blocking any requests to these API paths that don’t have a valid NaCl signature.
If there are no API keys configured as indicated by web_auth_strict = true being shown in the starting server log message the external web server will only pass through requests to admin API paths that have a valid NaCl signature. If admin API keys are configured web_auth_strict = false will be shown on startup and the request will get sent through although it will still validate the signature for non-API based requests. If you are not using the Pritunl API and API keys were previously configured use the command sudo pritunl disable-admin-api to remove any existing API keys and configure the server to run with web_auth_strict.
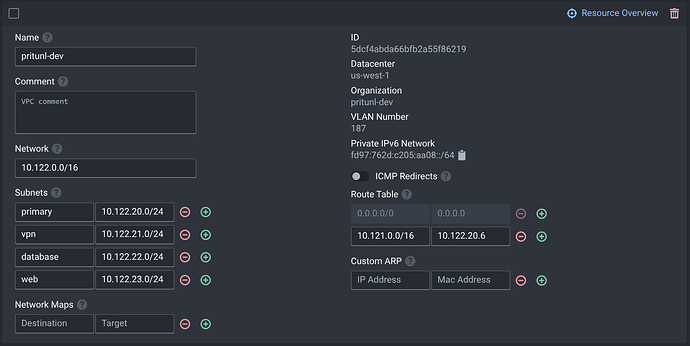
Pritunl Cloud Support
Pritunl Cloud a new self hosted declarative KVM virtualization platform is now supported in the Pritunl VPN server. This allows the VPC route management features in Pritunl to work on a Pritunl Cloud instance using the API.